Cursus
MongoDB Atlas requires multi-factor authentication (MFA) for all accounts. MFA helps prevent unauthorized access, even if someone steals your password, by requiring an additional verification step beyond your password. If you are new to Atlas, you will need to configure MFA during account setup.
This guide explains the available MFA options, including authenticator apps, Okta Verify, security keys and biometrics, and email verification. You will learn:
- Why MFA strengthens MongoDB Atlas security beyond passwords
- How to configure MFA for social login and Atlas credentials
- Available MFA methods and when to use each one
- Best practices for maintaining secure authentication
Why MFA Matters for MongoDB Atlas
Your MongoDB Atlas database contains sensitive information that attackers can target. Relying on a single password leaves your account vulnerable because a compromised password gives an attacker complete access to your data.
To reduce this risk, MFA strengthens your security by adding an additional verification step. This additional verification step protects you from common threats such as credential stuffing, where attackers try passwords leaked from other services to access your MongoDB Atlas account. It also helps prevent phishing attacks, since a stolen password alone is not enough to sign in.
Beyond security, MFA is also important for compliance. Many industry standards require multi-factor authentication for systems that store or process sensitive information. Using MFA on your MongoDB Atlas account helps you meet these requirements.
Lastly, the consequences of unauthorized access can be severe. Attackers can delete collections, modify or steal records, expose customer data, or even hold your information for ransom. They may also misuse your database resources to launch attacks on other systems, which can leave you with unexpected costs and legal risks.
Understanding Your MFA Options in MongoDB Atlas
How you configure MFA in Atlas depends on the sign-up method you used. Different authentication methods manage MFA settings in different places.
MongoDB Atlas supports two authentication methods:
- Atlas credentials: If you sign up with an email and password, you configure MFA directly through the MongoDB Atlas UI. Atlas provides multiple MFA methods you can choose from.
- Federation: Your MFA is managed through your identity provider, not MongoDB Atlas. Federation includes:
- Social login: If you sign up with Google or GitHub, you manage your MFA through your account settings with those providers. Any two-step verification you configure there automatically applies to your MongoDB Atlas login.
- SAML SSO: If your organization uses SAML SSO, such as Okta or Azure AD, your administrator enforces MFA and specific authentication methods at the organization level through your identity provider's settings.
Set Up MFA With Social Login
Your MFA setup for federated login depends on which login method you use with MongoDB Atlas.
Log in with Google
If you signed up and subsequently log in using Google, your MFA is managed through your Google account settings, not MongoDB Atlas. Any two-step verification methods you configure in Google automatically apply to your Atlas login.
To configure Google's two-step verification, see Turn on 2-Step Verification.
Log in with GitHub
If you signed up and subsequently log in using GitHub, your MFA is managed through your GitHub account settings, not MongoDB Atlas.
To configure GitHub's two-factor authentication, see Configuring two-factor authentication.
Set Up MFA With Atlas Credentials
If you signed up with an email and password, you can configure MFA directly through the MongoDB Atlas UI. Atlas provides multiple MFA options.
To configure MFA, follow these steps:
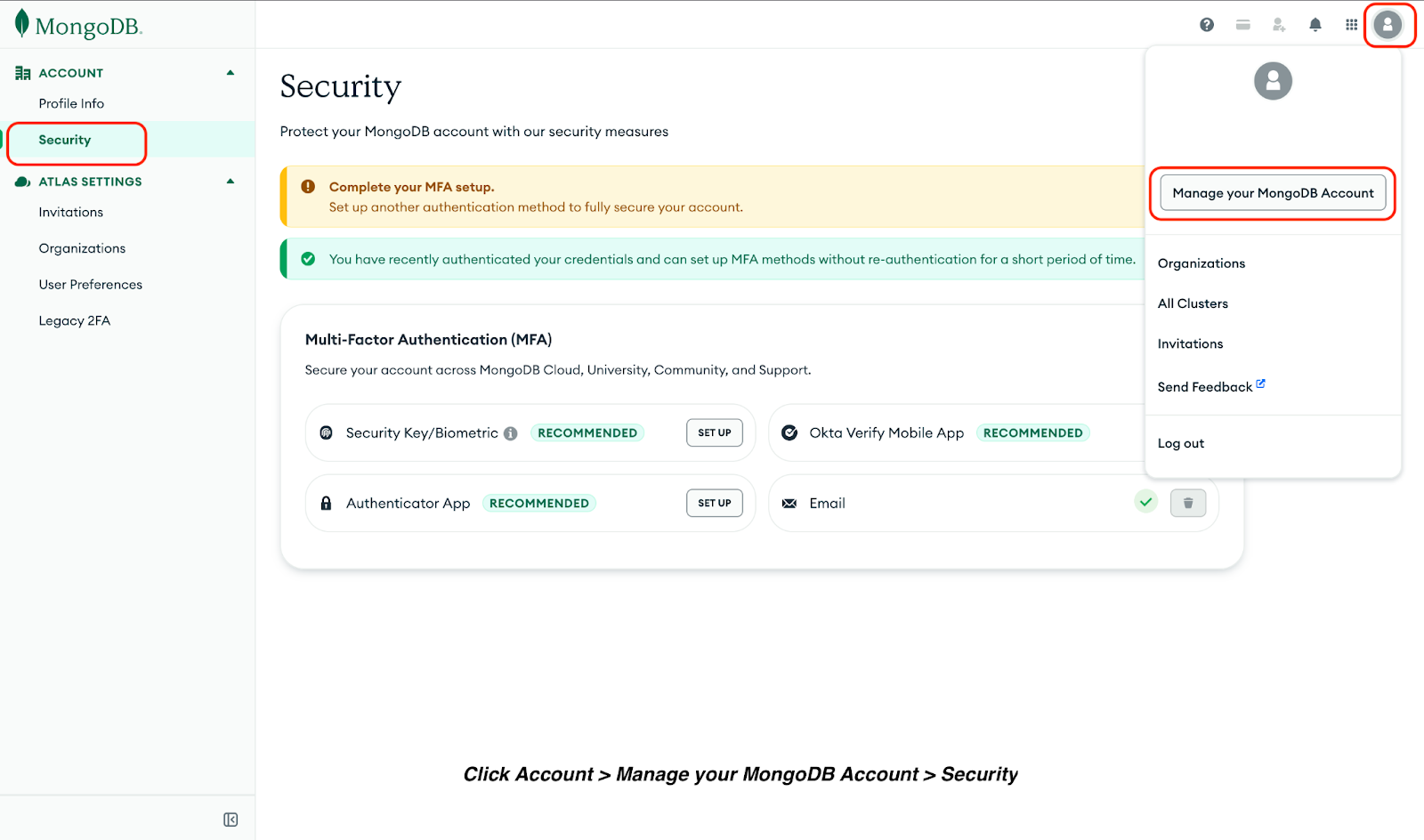
- Click Account > Manage your MongoDB Account > Security.
- Choose one of the available MFA methods:
- Security Key/Biometric
- Okta Verify Mobile App
- Authenticator App
Security key/biometric
Security Key/Biometric authentication includes Fast IDentity Online 2 (FIDO2) compliant MFA methods such as Windows Hello or Apple Touch ID.
To set up Security Key/Biometric MFA:
- Click SET UP in the Security Key/Biometric section.
- Verify your identity using an existing authentication method.
- Click Enroll and follow the system instructions to register your security key or biometric device.
Okta Verify mobile app
Okta Verify is a mobile authentication app that generates time-based one-time password (TOTP) and sends push notifications to approve login attempts.
To set up the Okta Verify Mobile App:
- Click SET UP in the Okta Verify Mobile App section.
- Verify your identity using an existing method.
- Download the Okta Verify app from the App Store or Google Play.
- Open the app and scan the QR code displayed on your screen.
- Enter the verification code from the app to complete enrollment.
Authenticator app
Authenticator apps, such as Google Authenticator, Microsoft Authenticator, and Authy, generate TOTP on your mobile device. To set up an authenticator app:
- Click SET UP in the Authenticator App section.
- Verify your identity using an existing method.
- Download an authenticator app from the App Store or Google Play Store.
- Follow the instructions on the download app.
MongoDB Atlas sends a one-time code to your registered email address each time you log in.
This method provides basic security without requiring additional apps or devices. When using this method, set up MFA for your email inbox access to maintain strong security.
Best Practices for MFA Security
Configure at least two MFA methods other than email to maintain access if one becomes unavailable or you lose access to it. This prevents you from being locked out of your account.
Also, your authenticator app provides recovery codes after setting them up. Download these codes and store them securely in a password manager, encrypted location, or cloud backup. Also, never save them in plain text files or share them with others.
Verification codes and recovery codes are single-use credentials. Treat them like passwords and never share them via email, chat, or phone.
Note: MongoDB support will never ask for your verification codes at login time.
Finally, update your MFA settings immediately when you change devices. Remove old devices from your account and re-register your new phone or security key to prevent unauthorized access through lost or stolen devices.
Key Takeaways
- MFA is mandatory for all MongoDB Atlas accounts.
- Configure at least two MFA methods for account recovery.
- Security keys and biometric authentication provide phishing-resistant protection.
- Store recovery codes securely and update MFA settings when changing devices.
FAQs
What happens if I lose access to my MFA device?
Use your recovery codes or cloud backup to regain access, then reconfigure MFA with your new device.
Can I use multiple MFA methods simultaneously?
Yes. MongoDB Atlas allows you to configure multiple MFA methods. The system will prompt you to choose which method to use during login.
Does MFA slow down my login process?
MFA adds 5-10 seconds to your login process. Security keys and biometric methods are typically faster than email verification.
Will MFA affect my MongoDB Atlas database access?
No. MFA only applies to logging into the Atlas UI. However, if you use Workforce Identity Federation for database access, you can enforce MFA through your identity provider.
Will MFA affect my MongoDB Atlas API access?
MFA applies only to the Atlas UI login. API access uses separate authentication with Atlas API keys or service accounts and is not affected by MFA settings.
